SIEM vs. EDR: When Visibility Meets Response Speed

09 Feb 2026
SIEM vs. EDR: When Visibility Meets Response Speed
Amidst increasing ransomware attacks, increasingly convincing phishing, and unpredictable zero-day exploits, companies are no longer asking, “Do we need a security solution?”
The question now becomes: “What kind of solutions are truly relevant to protect our business?”
The debate that often arises is: SIEM or EDR?
In fact, when viewed from a modern approach such as that developed by SentinelOne, the two are not meant to be compared as substitutes for one another. Rather, SIEM and EDR are two complementary layers of protection
SIEM: Seeing the Big Picture

SIEM (Security Information and Event Management) functions as a center for collecting and analyzing security data from various sources, such as:
-
Server
-
Application
-
Firewall
-
Network device
-
Endpoint
Think of SIEM as a central control room. All logs and activities are collected in one place, then analyzed to find unusual patterns, suspicious activity, or potential policy violations.
The advantages of SIEM include:
-
Providing comprehensive visibility into IT infrastructure
-
Correlating data from multiple systems
-
Supporting audit and compliance requirements
-
Assisting SOC teams in conducting investigations based on historical data
However, SIEM essentially focuses on analysis and alerting. It notifies you that there are indications of a problem but does not always stop it immediately.
EDR: Moving Quickly at the Point of Attack

Unlike SIEM, EDR (Endpoint Detection and Response) works directly on user devices and servers.
From employee laptops and production servers to developer workstations, everything is monitored in real time.
Modern EDR approaches such as those developed by SentinelOne emphasize:
-
Behavior-based detection, not just signatures
-
Continuous monitoring of process activity
-
Automatic responses, such as endpoint isolation or termination of malicious processes
If SIEM is the command center, then EDR is the rapid response team in the field. When a threat is detected, the system can take immediate action without having to wait for a lengthy manual process.
SIEM & EDR solutions from SentinelOne
-
Singularity XDR (EDR Solution)
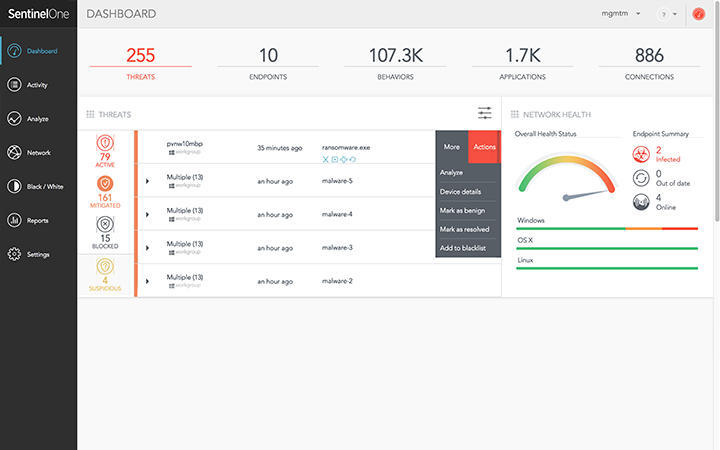
Singularity XDR provides:
-
AI-based detection and behavioral analysis
-
Automated response including ransomware remediation and rollback
-
Visibility across endpoints, cloud workloads, and identities
-
Storyline™ technology to understand the full chronology of an attack
With this approach, threats can be stopped quickly and measurably.
- Singularity Data Lake (Modern SIEM Approach)
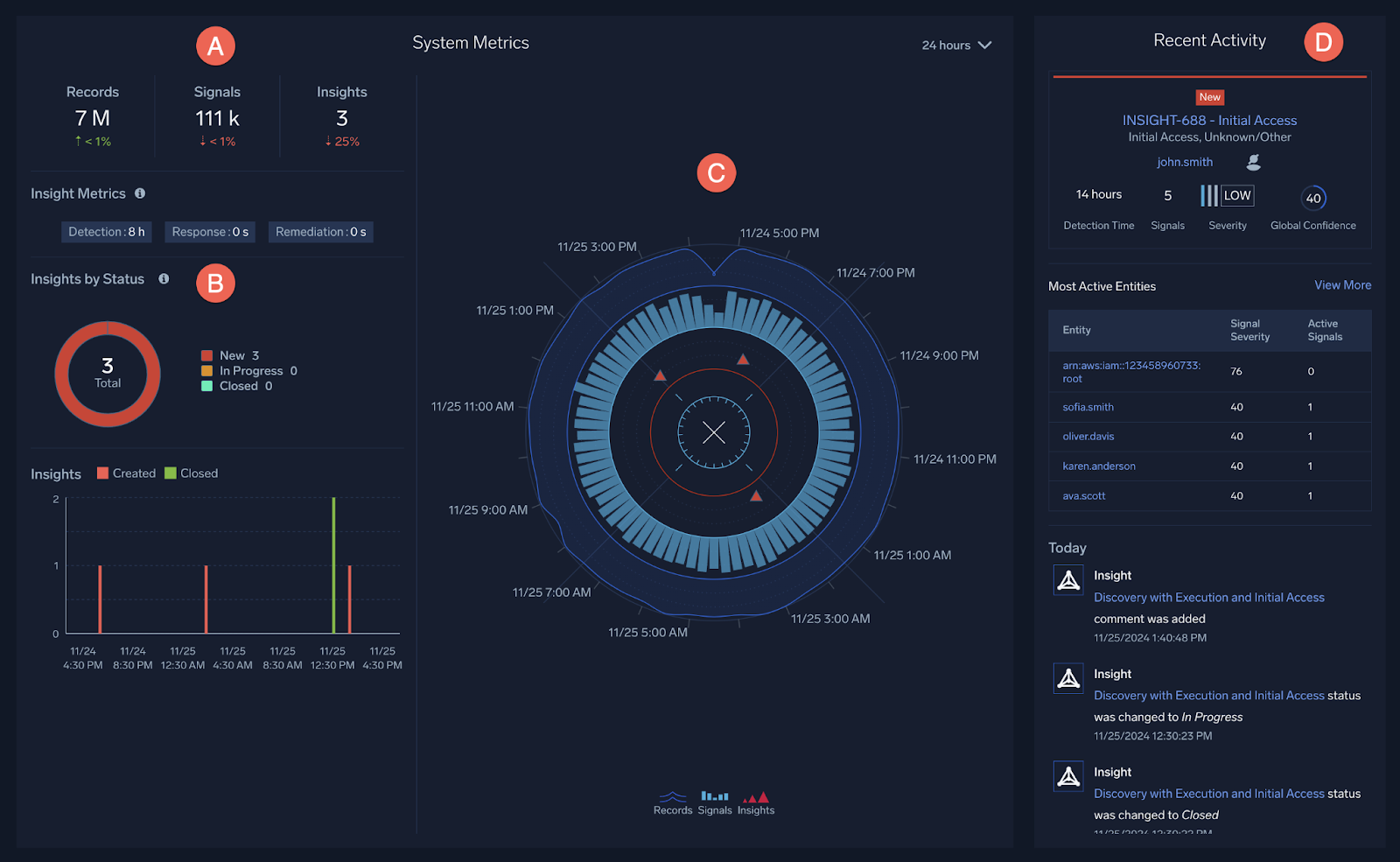
As an evolution of traditional SIEM, Singularity Data Lake offers:
-
Cloud-based large-scale data storage
-
Cross-endpoint, cloud, and network data correlation
-
Threat hunting capabilities with fast queries
-
Direct integration with XDR for unified response
With this integration, data is not only collected and analyzed, but also directly linked to automated response capabilities.
Why is this combination important?
Today's cyberattack often start from a single endpoint and spread across the entire network in a short period of time. By combining SIEM and EDR:
-
Technical details of endpoints can be captured in real time
-
The data is linked to a broader system context
-
Security teams gain a complete picture and the ability to take action
As a result, organizations not only know that threats exist, but are also able to respond quickly and appropriately.
Perkom: Appropriate and Targeted Implementation
As a technology partner, Perkom helps companies implement SentinelOne-based security solutions strategically and measurably.
Our approach includes:
-
Security requirements and risk analysis
-
Integrated architecture design
-
Efficient and scalable implementation
-
Optimization without adding unnecessary complexity
The goal is simple: to build a defense system that is reasonable, effective, and ready to face real threats.
Author: Ghea Devita
Marketing Communication PT Perkom Indah Murni